The IPDS or Intrusion and Prevention Detection System section within the IPDS module permits to configure and set protection rules at System or Farm service level.IPDS is a module which implements a group of techniques designed to detect, analyze and block network attacks.
On the other hand, RBL or Real-time Blackhole Lists are community-based, central repositories for IP Reputation. RBLs are most commonly used to identify web-based comment spam, or network attackers. The repository maintain a list of IP that can be blocked (blacklisted) on servers, thus lowering the probability of an attack to our servers.
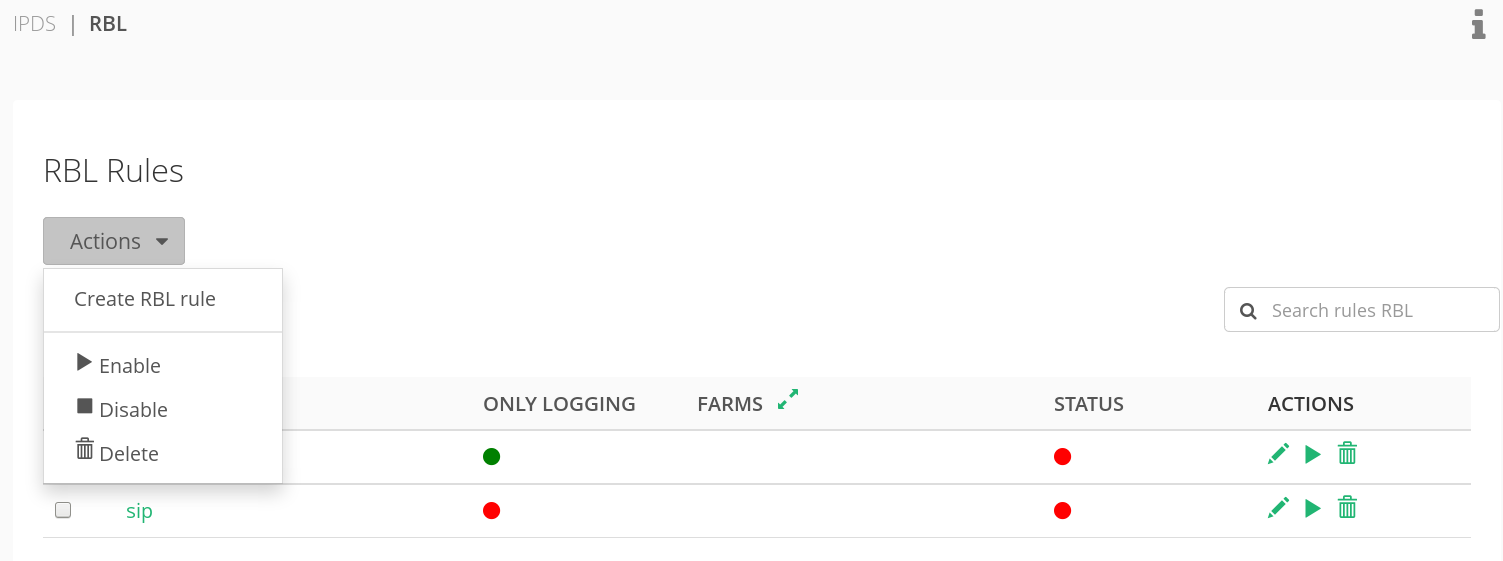
This section shows a list of your actual RBL rules.
The fields of the list are:
NAME. The unique describing name of the rule.
Only Logging. If activated, the rule has no real effect, just writes output to the syslog for debugging purposes.
Farms. List of farms in which the rule is applied.
Status. Shows if the rule is up and running or stopped.
Actions. The three elements under Actions column permit to edit, to run/stop the rule or to delete it.
Actions menu, also allows to add and configure a new RBL Rule.
Check out the video of RBL.
Please, follow this link for further information about Creating New RBL Rules, or Updating an RBL Rule