POSTED ON 16 February, 2017
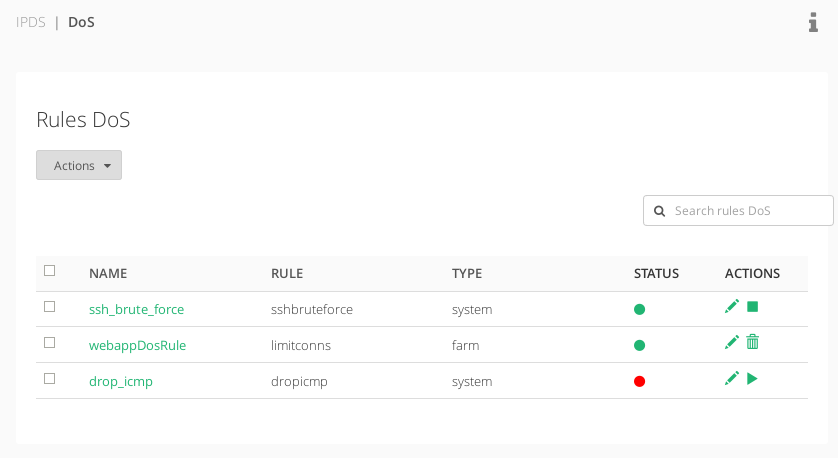
The DoS or Denial of Service section within the IPDS module permits to configure and set protection rules at System or Farm service level.
The System rules are preloaded but the Farm rules should be configured by the administrator. This section shows the available lists:
NAME. Rule name identification. Click on it to enter to the editing form.
RULE. It’s the type of the rule. The different options will be:
- sshbruteforce. Protect the system against the SSH password bruteforce.
- dropicmp. Protect the system against ICMP flooding attacks.
- limitsec: Connection limit per second. Protect the farm service limiting the number of connections per second accessing to the service.
- limitconns: Total connections limit per source IP. Protect the farm service limiting the number of connections per source IP accessing to the service.
- bogustcpflags: Check bogus TCP flags. Protect the farm service with bogus TCP flags packets.
- limitrst: Limit RST request per second. Protect the farm service of RST requests for TCP connections by limiting the RST packets per seconds accepted.
TYPE. System for global system rules and Farm for rules to be defined dedicated to certain farm services.
STATUS. Red for unused rules and Green for applied ones.
ACTIONS. Allowed actions for the status of the DoS rules:
- Edit. To modify the rule global settings or assign a farm service if needed.
- Delete. Remove a created farm service rule.
- Enable. To activate a system rule.
- Disable. To deactivate a system rule.
- Create DoS rule. Create a new rule to be assigned to certain farm services.
Next step, create a custom DoS rule.
Documentation under the terms of the GNU Free Documentation License.